Introduction
Mobile and web apps handle payments, identity data, and private messages. They manage business transactions and cloud access too. That makes them very attractive targets for attackers.
Attackers today do not just use simple malware anymore. They automate login attempts and manipulate APIs. They inject malicious code and reverse engineer apps to bypass restrictions.
I worked on several Android security reviews for small development teams. I noticed the same problem every single time. Most apps depended on basic static controls like simple rate limiting and manual monitoring dashboards.
Those controls blocked obvious attacks just fine. But they failed completely when attacker behavior changed slightly. When login abuse came from rotating IP addresses instead of one source, the protection layer missed it entirely.
That gap is exactly why AI in App Security has become so important.
Why Static Security Models Struggle
Traditional application security relies on signature based malware detection. It uses rule based fraud prevention and static code analysis tools. Web application firewalls and manual penetration testing round out the approach.
These methods work well against known attack signatures. The weakness appears when attackers simply change their behavior patterns. They stop repeating identical payloads and start doing something slightly different.
A basic rule might block an IP address after five failed login attempts. An automated attack distributing attempts across thousands of IP addresses bypasses that rule completely. The attack is still visible in aggregate behavior but not in isolated events.
Static logic only evaluates isolated events. That is the fundamental problem.
Modern apps are also highly dynamic. They interact with cloud APIs, third party SDKs, payment processors, and authentication providers. Each integration increases complexity and expands the potential attack surface.
What AI in App Security Actually Involves
AI in App Security uses machine learning models to analyze large volumes of application data. It detects abnormal patterns that may indicate malicious activity. Instead of relying on predefined rules it evaluates probability.
These systems establish a baseline of normal user behavior first. They compare every new session against that baseline continuously. Then they assign dynamic risk scores to each session in real time.
When risk exceeds a defined threshold automated mitigation steps trigger immediately. The system does not look for known signatures. It looks for behavior that deviates from what is normal for that specific user.
For example imagine a user account logging in from a device never seen before. The login comes from a distant geography at an unusual hour. The user immediately initiates a high value transaction right after logging in.
No single action violates any rule here. But a behavioral model classifies this as high risk immediately. That is the power of AI over static rules.
How AI Threat Detection Systems Are Built
Telemetry and Data Collection
Effective AI models depend on structured reliable data streams. Common inputs include authentication logs, device fingerprint attributes, and IP metadata. API request frequency, transaction details, and behavioral biometrics also feed into the system.
Data quality directly affects model performance. I worked on one API audit where incomplete logging was preventing accurate anomaly detection. Session metadata was not being stored consistently anywhere.
After standardizing log formats and enabling full request tracing detection accuracy improved significantly. The data was always there. It just needed to be captured properly.
Feature Engineering
Raw logs get transformed into measurable indicators. These include login velocity across accounts, distance between consecutive login locations, and session duration anomalies. Device consistency scores and unusual API call sequences also matter.
Feature engineering determines whether a model captures meaningful patterns or just noise. Poorly selected features increase false positives dramatically. Getting this step right is critical.
Model Training
Several machine learning approaches are used in app security AI. Supervised learning handles fraud classification when labeled attack data exists. Unsupervised anomaly detection identifies unknown patterns without needing labeled examples.
Deep learning models classify malware behavior effectively. Ensemble techniques combine multiple signals for better accuracy. Most production systems combine supervised and unsupervised approaches together.
Real Time Inference Layer
Once trained, models deploy within the application infrastructure. Every incoming request gets evaluated in milliseconds. The output is usually a risk score rather than a simple yes or no decision.
Latency matters enormously here. In one deployment I reviewed, enabling full behavioral scoring increased authentication time by over 100 milliseconds. Reducing feature complexity and optimizing the inference pipeline brought response time back within acceptable limits.
Automated Mitigation Mechanisms
Detection without response has very limited value. AI based systems trigger proportional responses based on calculated risk scores. Low risk gets through normally. High risk gets challenged.
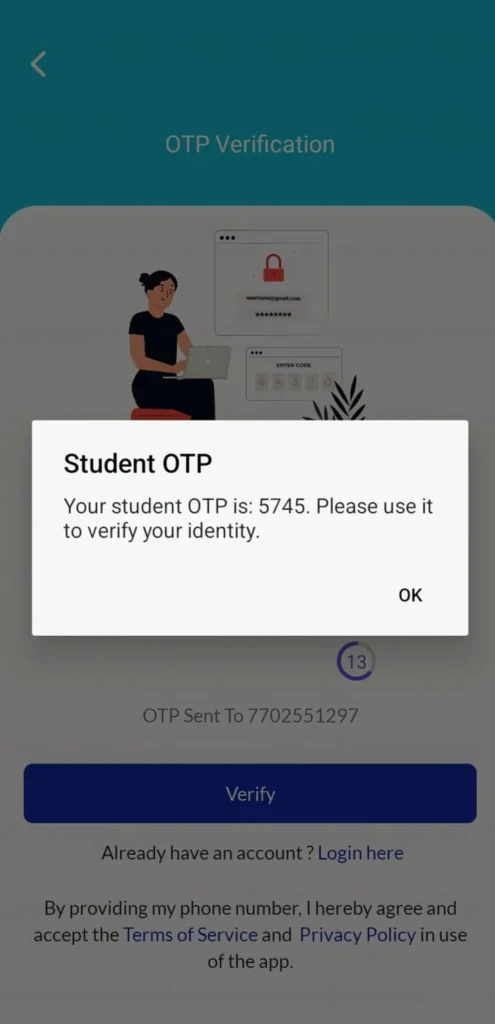
Common responses include multi-factor authentication challenges and temporary account lockouts. Transaction verification steps, API throttling, and additional identity validation are also used. The response always matches the level of detected risk.
Threat Categories AI Handles Effectively
Credential Stuffing
Automated login attempts using breached credentials are extremely common today. AI models identify abnormal login velocity across multiple accounts. They also catch shared device patterns and coordinated behavior that rule based systems completely miss.
Bot Traffic and Automation Abuse
Advanced bots try to simulate human interaction convincingly. Behavioral models analyze interaction timing, gesture variability, and navigation patterns. They distinguish automation from legitimate usage with high accuracy.
API Abuse
Modern applications depend heavily on APIs. AI based API security monitors deviations from expected request flows. If a client calls endpoints in an unusual sequence or manipulates parameters abnormally the system flags it immediately.
Mobile App Tampering
Mobile security solutions use behavioral monitoring to identify runtime manipulation. Debugging attempts and modified application binaries also get detected. This protects apps from reverse engineering attacks.
Transaction Fraud
Financial apps use anomaly detection models that evaluate transaction value and user history. Device trust level and geographic consistency also factor into the risk calculation. Instead of rejecting transactions outright systems apply step up verification for suspicious activity.
Privacy and Compliance Considerations
AI based threat detection requires behavioral data to function. Organizations must ensure compliance with applicable data protection regulations. This is not optional.
Key practices include minimizing unnecessary data collection and anonymizing sensitive identifiers where possible. Clear retention policies and documented automated decision logic are also required. Security improvements should never come at the cost of user privacy.
Operational Challenges to Understand
False Positives
Aggressive models sometimes block legitimate users accidentally. Monitoring precision and recall metrics constantly is essential. Regular model tuning reduces unnecessary friction for real users.
Model Drift
User behavior changes over time naturally. Seasonal usage spikes, product updates, and geographic expansion all alter behavioral baselines. Periodic retraining prevents accuracy from degrading over time.
Infrastructure Cost
Real time inference consumes significant computational resources. Scalable cloud deployment and model optimization are necessary to control costs. This is a real operational expense that teams must plan for.
Best Practices for Implementation
Conduct detailed threat modeling before selecting any solution. Standardize logging across all services from the very beginning. Combine AI detection with rule based safeguards always.
Continuously evaluate false positive rates and adjust accordingly. Retrain models regularly using recent behavioral data. Maintain human oversight for all critical security decisions.
AI enhances security best when integrated into a layered defense strategy. It should never replace foundational security controls. It should strengthen them.
Also Read: Clear Cache vs Clear Data: What Really Happens on Android
Also Read: How Voice Assistants Understand Accents Using Machine Learning (Complete Guide)
Conclusion
AI in App Security enables applications to detect behavioral anomalies that static systems consistently miss. It catches automation abuse, credential attacks, and fraud patterns in real time. By analyzing aggregated behavior instead of isolated events it provides adaptive protection.
But successful implementation requires high quality telemetry and careful feature design. Performance optimization, privacy compliance, and continuous monitoring are all essential. AI is one powerful component of a broader security architecture.
Organizations that treat it as the entire solution will be disappointed. Organizations that treat it as one strong layer in a multi layered defense will see real results. That difference in approach determines everything.
FAQ’s
1. What is AI in App Security?
AI in App Security uses machine learning models to analyze application data and detect abnormal behavior indicating malicious activity. It evaluates behavioral patterns instead of just checking against known signatures. This allows it to catch attacks that traditional rule based systems completely miss.
2. Can AI eliminate the need for traditional security controls?
No it cannot and should not try to. Encryption, secure coding practices, authentication controls, and manual security testing all remain essential. AI strengthens detection capabilities but never replaces foundational security safeguards.
3. How does AI detect credential stuffing attacks?
Behavioral models identify abnormal login velocity across multiple accounts simultaneously. They also catch unusual device patterns and coordinated attempts that differ from legitimate user activity. The aggregate pattern reveals the attack even when individual events look normal.
4. Does AI based threat detection slow down applications?
It can increase latency if poorly optimized. Proper infrastructure design and efficient model deployment keep performance impact minimal. In well optimized systems the added protection comes with almost no noticeable speed difference.
5. Is AI in App Security suitable for smaller applications?
Yes especially through managed cloud based security services. These provide scalable behavioral monitoring without requiring heavy infrastructure investment. Small teams can access enterprise grade protection without building everything from scratch.